Security
At Komo, we take security and privacy seriously. Let's explore the ways in which we safeguard your data.

YOUR DATA: PROTECTED BY DEFAULT
At Komo, we take security and privacy seriously. Let's explore the ways in which we safeguard your data.
We implement industry-standard encryption protocols that protect all data at rest on our servers from unauthorized access.
Data is transferred between our customers’ browser and servers or between systems using HTTPS to ensure data is encrypted in transit.
We prioritize product security by adhering to industry best practices in design, conducting regular assessments throughout development.
We regularly hire third-party security experts for audits and annual penetration testing to find and fix system vulnerabilities.








product security


Control usability with user access levels

Password protection guidance
Robust Infrastructure Security
Our Commitments to data security




What our clients are saying
We had a great time putting together our Komo campaign for Froth Town 2022. The Scratch and Win game was so fun and provided us an opportunity to give away customer incentives to purchase tickets to our festival. The activation worked so well and we reached our goal of entries without any digital spend. Our team is very much looking forward to using the platform again in the future as the need for creative ways to market continues to increase year on year.

Co-Founder & Director at Bar Pop
FAQS
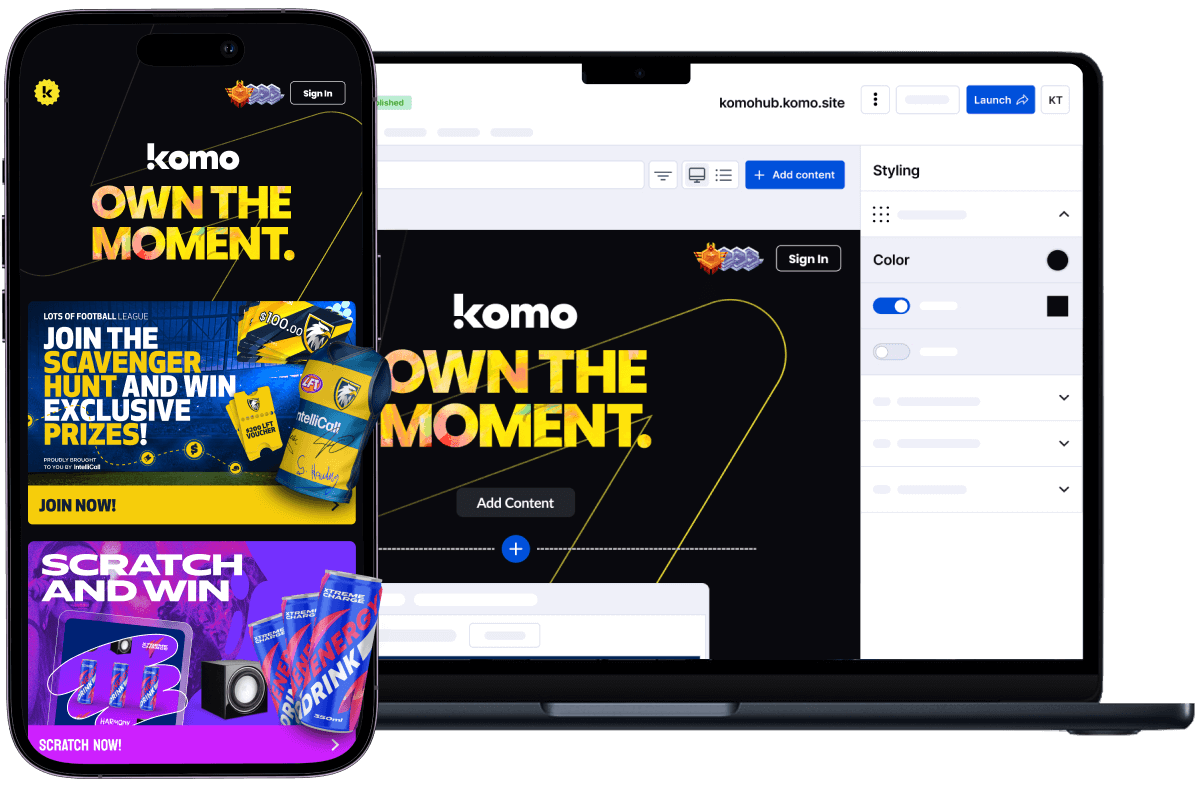
WELL, WHAT ARE YOU WAITING FOR?
Ready to learn more? Book a personalized demo and we’ll introduce you to our all-in-one customer engagement platform.